Enabling scanning for non-provider patterns
You can enable scanning for non-provider patterns. Non-provider patterns correspond to secrets such as private keys and they have a higher ratio of false positives.
For more information about non-provider patterns, see "Supported secret scanning patterns."
Enabling detection of non-provider patterns for a repository
-
On GitHub, navigate to the main page of the repository.
-
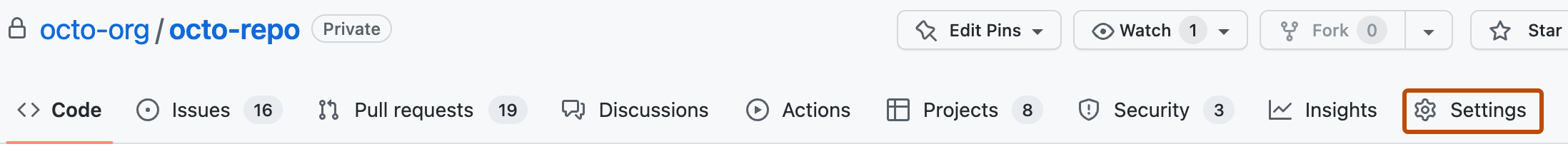
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security.
-
Under Secret scanning, to the right of "Non-provider patterns", click Enable.
Enabling detection of non-provider patterns for an organization
You can enable scanning for non-provider patterns at the organization level using the GitHub-recommended security configuration or by applying a custom security configuration. For more information, see Applying the GitHub-recommended security configuration in your organization and Creating a custom security configuration.