About environments
Environments are used to describe a general deployment target like production, staging, or development. When a GitHub Actions workflow deploys to an environment, the environment is displayed on the main page of the repository. For more information about viewing deployments to environments, see Viewing deployment history.
You can configure environments with protection rules and secrets. When a workflow job references an environment, the job won't start until all of the environment's protection rules pass. A job also cannot access secrets that are defined in an environment until all the deployment protection rules pass.
Optionally, you can bypass an environment's protection rules and force all pending jobs referencing the environment to proceed. For more information, see Reviewing deployments.
Deployment protection rules
Deployment protection rules require specific conditions to pass before a job referencing the environment can proceed. You can use deployment protection rules to require a manual approval, delay a job, or restrict the environment to certain branches. You can also create and implement custom protection rules powered by GitHub Apps to use third-party systems to control deployments referencing environments configured on GitHub.
Third-party systems can be observability systems, change management systems, code quality systems, or other manual configurations that you use to assess readiness before deployments are safely rolled out to environments.
Note
Any number of GitHub Apps-based deployment protection rules can be installed on a repository. However, a maximum of 6 deployment protection rules can be enabled on any environment at the same time.
Required reviewers
Use required reviewers to require a specific person or team to approve workflow jobs that reference the environment. You can list up to six users or teams as reviewers. The reviewers must have at least read access to the repository. Only one of the required reviewers needs to approve the job for it to proceed.
You also have the option to prevent self-reviews for deployments to protected environments. If you enable this setting, users who initiate a deployment cannot approve the deployment job, even if they are a required reviewer. This ensures that deployments to protected environments are always reviewed by more than one person.
For more information on reviewing jobs that reference an environment with required reviewers, see Reviewing deployments.
Wait timer
Use a wait timer to delay a job for a specific amount of time after the job is initially triggered. The time (in minutes) must be an integer between 1 and 43,200 (30 days). Wait time will not count towards your billable time.
Deployment branches and tags
Use deployment branches and tags to restrict which branches and tags can deploy to the environment. Below are the options for deployment branches and tags for an environment:
-
No restriction: No restriction on which branch or tag can deploy to the environment.
-
Protected branches only: Only branches with branch protection rules enabled can deploy to the environment. If no branch protection rules are defined for any branch in the repository, then all branches can deploy. For more information about branch protection rules, see About protected branches.
Note
Deployment workflow runs triggered by tags with the same name as a protected branch and forks with branches that match the protected branch name cannot deploy to the environment.
-
Selected branches and tags: Only branches and tags that match your specified name patterns can deploy to the environment.
If you specify
releases/*as a deployment branch or tag rule, only a branch or tag whose name begins withreleases/can deploy to the environment. (Wildcard characters will not match/. To match branches or tags that begin withrelease/and contain an additional single slash, userelease/*/*.) If you addmainas a branch rule, a branch namedmaincan also deploy to the environment. For more information about syntax options for deployment branches, see the RubyFile.fnmatchdocumentation.Note
Name patterns must be configured for branches or tags individually.
Allow administrators to bypass configured protection rules
By default, administrators can bypass the protection rules and force deployments to specific environments. For more information, see Reviewing deployments.
Alternatively, you can configure environments to disallow bypassing the protection rules for all deployments to the environment.
Custom deployment protection rules
Note
Custom deployment protection rules are currently in beta and subject to change.
You can enable your own custom protection rules to gate deployments with third-party services. For example, you can use services such as Datadog, Honeycomb, and ServiceNow to provide automated approvals for deployments to GitHub. For more information, see Creating custom deployment protection rules.
Once custom deployment protection rules have been created and installed on a repository, you can enable the custom deployment protection rule for any environment in the repository. For more information about configuring and enabling custom deployment protection rules, see Configuring custom deployment protection rules.
Environment secrets
Secrets stored in an environment are only available to workflow jobs that reference the environment. If the environment requires approval, a job cannot access environment secrets until one of the required reviewers approves it. For more information about secrets, see Using secrets in GitHub Actions.
Note
Workflows that run on self-hosted runners are not run in an isolated container, even if they use environments. Environment secrets should be treated with the same level of security as repository and organization secrets. For more information, see Security hardening for GitHub Actions.
Environment variables
Variables stored in an environment are only available to workflow jobs that reference the environment. These variables are only accessible using the vars context. For more information, see Store information in variables.
Creating an environment
To configure an environment in a personal account repository, you must be the repository owner. To configure an environment in an organization repository, you must have admin access.
-
On GitHub, navigate to the main page of the repository.
-
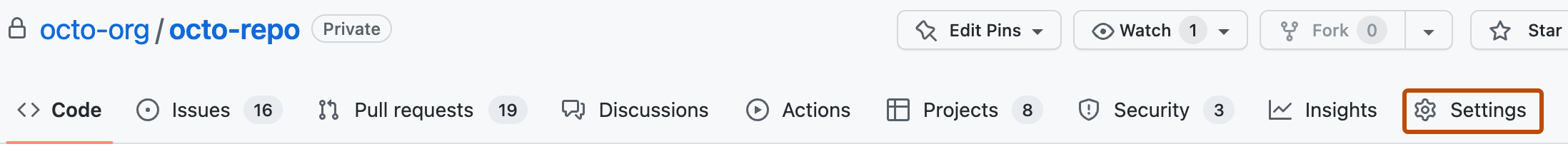
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the left sidebar, click Environments.
-
Click New environment.
-
Enter a name for the environment, then click Configure environment. Environment names are not case sensitive. An environment name may not exceed 255 characters and must be unique within the repository.
-
Optionally, specify people or teams that must approve workflow jobs that use this environment. For more information, see Required reviewers.
- Select Required reviewers.
- Enter up to 6 people or teams. Only one of the required reviewers needs to approve the job for it to proceed.
- Optionally, to prevent users from approving workflows runs that they triggered, select Prevent self-review.
- Click Save protection rules.
-
Optionally, specify the amount of time to wait before allowing workflow jobs that use this environment to proceed. For more information, see Wait timer.
- Select Wait timer.
- Enter the number of minutes to wait.
- Click Save protection rules.
-
Optionally, disallow bypassing configured protection rules. For more information, see Allow administrators to bypass configured protection rules.
- Deselect Allow administrators to bypass configured protection rules.
- Click Save protection rules.
-
Optionally, enable any custom deployment protection rules that have been created with GitHub Apps. For more information, see Custom deployment protection rules.
- Select the custom protection rule you want to enable.
- Click Save protection rules.
-
Optionally, specify what branches and tags can deploy to this environment. For more information, see Deployment branches and tags.
-
Select the desired option in the Deployment branches dropdown.
-
If you chose Selected branches and tags, to add a new rule, click Add deployment branch or tag rule
-
In the "Ref type" dropdown menu, depending on what rule you want to apply, click Branch or Tag.
-
Enter the name pattern for the branch or tag that you want to allow.
Note
Name patterns must be configured for branches or tags individually.
-
Click Add rule.
-
-
Optionally, add environment secrets. These secrets are only available to workflow jobs that use the environment. Additionally, workflow jobs that use this environment can only access these secrets after any configured rules (for example, required reviewers) pass. For more information, see Environment secrets.
- Under Environment secrets, click Add Secret.
- Enter the secret name.
- Enter the secret value.
- Click Add secret.
-
Optionally, add environment variables. These variables are only available to workflow jobs that use the environment, and are only accessible using the
varscontext. For more information, see Environment variables.- Under Environment variables, click Add Variable.
- Enter the variable name.
- Enter the variable value.
- Click Add variable.
You can also create and configure environments through the REST API. For more information, see REST API endpoints for deployment environments, REST API endpoints for GitHub Actions Secrets, REST API endpoints for GitHub Actions variables, and REST API endpoints for deployment branch policies.
Running a workflow that references an environment that does not exist will create an environment with the referenced name. If the environment is created from running implicit page builds (for example, from a branch or folder source), the source branch will be added as a protection rule to the environment. Otherwise, the newly created environment will not have any protection rules or secrets configured. Anyone that can edit workflows in the repository can create environments via a workflow file, but only repository admins can configure the environment.
Deleting an environment
To configure an environment in a personal account repository, you must be the repository owner. To configure an environment in an organization repository, you must have admin access.
Deleting an environment will delete all secrets and protection rules associated with the environment. Any jobs currently waiting because of protection rules from the deleted environment will automatically fail.
-
On GitHub, navigate to the main page of the repository.
-
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the left sidebar, click Environments.
-
Next to the environment that you want to delete, click .
-
Click I understand, delete this environment.
You can also delete environments through the REST API. For more information, see REST API endpoints for repositories.
How environments relate to deployments
When a workflow job that references an environment runs, it creates a deployment object with the environment property set to the name of your environment. As the workflow progresses, it also creates deployment status objects with the environment property set to the name of your environment, the environment_url property set to the URL for environment (if specified in the workflow), and the state property set to the status of the job.
You can access these objects through the REST API or GraphQL API. You can also subscribe to these webhook events. For more information, see REST API endpoints for repositories, Objects (GraphQL API), or Webhook events and payloads.
Next steps
GitHub Actions provides several features for managing your deployments. For more information, see Deploying with GitHub Actions.