About enabling delegated bypass for push protection
Note
Delegated bypass for push protection is currently in beta and subject to change.
Delegated bypass for push protection lets you:
- Define contributors who can bypass push protection.
- Adds an approval process for other contributors.
For more information, see About delegated bypass for push protection.
When you enable this feature, you will create a bypass list of roles and teams who can manage requests to bypass push protection. If you don't already have appropriate teams or roles to use, you should create additional teams before you start.
Configuring delegated bypass for a repository
Note
If an organization owner configures delegated bypass at the organization-level, the repository-level settings are disabled.
-
On GitHub, navigate to the main page of the repository.
-
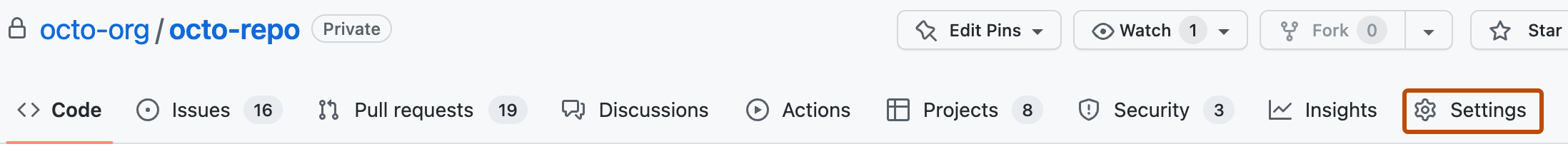
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under "Code security and analysis", find "GitHub Advanced Security."
-
Under "Push protection", to the right of "Who can bypass push protection for secret scanning", select the dropdown menu, then click Specific roles or teams.
-
Under "Bypass list", click Add role or team.
Note
When you add roles or teams to the "bypass list", these users will be granted the ability to bypass push protection, and they can also review and manage the requests from all other contributors to bypass push protection.
You can't add secret teams to the bypass list.
-
In the dialog box, select the roles and teams that you want to add to the bypass list, then click Add selected.
Configuring delegated bypass for an organization
-
On GitHub, navigate to the main page of the organization.
-
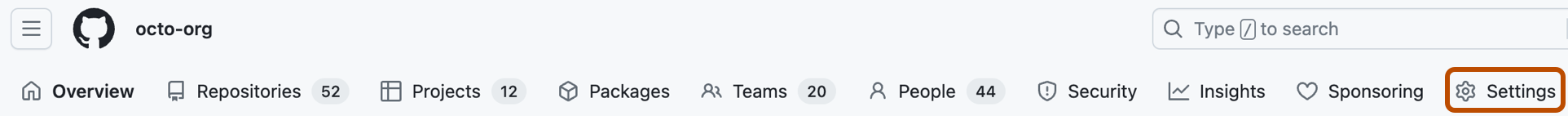
Under your organization name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under "Code security and analysis", find "GitHub Advanced Security."
-
Under "Push protection", to the right of "Who can bypass push protection for secret scanning", select the dropdown menu, then click Specific roles or teams.
-
Under "Bypass list", click Add role or team.
-
In the dialog box, select the roles and teams that you want to add to the bypass list, then click Add selected.