About Dependabot alerts for vulnerable dependencies
A vulnerability is a problem in a project's code that could be exploited to damage the confidentiality, integrity, or availability of the project or other projects that use its code. Vulnerabilities vary in type, severity, and method of attack.
Dependabot scans code when a new advisory is added to the GitHub Advisory Database or the dependency graph for a repository changes. When vulnerable dependencies are detected, Dependabot alerts are generated. For more information, see About Dependabot alerts.
If you have enabled Dependabot security updates for your repository, the alert may also contain a link to a pull request to update the manifest or lock file to the minimum version that resolves the vulnerability. For more information, see About Dependabot security updates.
You can enable or disable Dependabot alerts for:
- Your personal account
- Your repository
- Your organization
Additionally, you can use Dependabot auto-triage rules to manage your alerts at scale, so you can auto-dismiss or snooze alerts, and specify which alerts you want Dependabot to open pull requests for. For information about the different types of auto-triage rules, and whether your repositories are eligible, see About Dependabot auto-triage rules.
Managing Dependabot alerts for your personal account
You can enable or disable Dependabot alerts for all repositories owned by your personal account.
Enabling or disabling Dependabot alerts for existing repositories
- In the upper-right corner of any page on GitHub, click your profile photo, then click Settings.
- In the "Security" section of the sidebar, click Code security.
- Under "Code security", to the right of Dependabot alerts, click Disable all or Enable all.
- Optionally, to enable Dependabot alerts by default for new repositories that you create, in the dialog box, select "Enable by default for new repositories".
- Click Disable Dependabot alerts or Enable Dependabot alerts to disable or enable Dependabot alerts for all the repositories you own.
When you enable Dependabot alerts for existing repositories, you will see any results displayed on GitHub within minutes.
Enabling or disabling Dependabot alerts for new repositories
- In the upper-right corner of any page on GitHub, click your profile photo, then click Settings.
- In the "Security" section of the sidebar, click Code security.
- Under "Code security", to the right of Dependabot alerts, select Automatically enable for new repositories.
Managing Dependabot alerts for your repository
You can manage Dependabot alerts for your public, private or internal repository.
By default, we notify people with write, maintain, or admin permissions in the affected repositories about new Dependabot alerts. GitHub never publicly discloses insecure dependencies for any repository. You can also make Dependabot alerts visible to additional people or teams working on repositories that you own or have admin permissions for.
If you enable security and analysis features, GitHub performs read-only analysis on your repository.
Enabling or disabling Dependabot alerts for a repository
-
On GitHub, navigate to the main page of the repository.
-
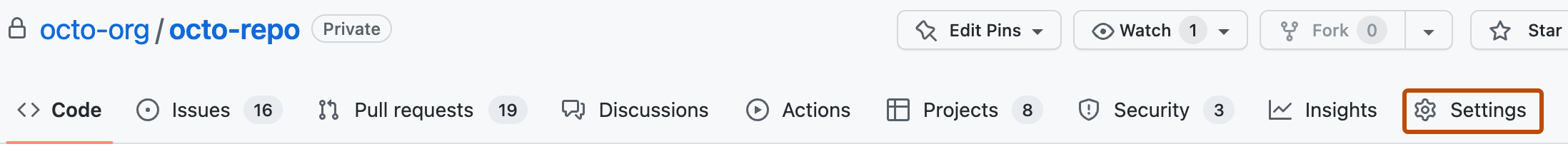
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security.
-
Under "Code security", to the right of Dependabot alerts, click Enable to enable alerts or Disable to disable alerts.
Managing Dependabot alerts for your organization
You can enable Dependabot alerts for all eligible repositories in your organization. For more information, see About enabling security features at scale.