About security findings
After you apply a security configuration to a repository, the enabled security features will likely raise security findings on that repository. These findings may show up as feature-specific alerts, or as automatically generated pull requests designed to keep your repositories secure. You can analyze the findings across the organization and make any necessary adjustments to your security configuration.
To best secure your organization, you should encourage contributors to review and resolve security alerts and pull requests. In addition, you can collaborate with contributors to fix historical security alerts, see Best practices for fixing security alerts at scale.
Finding repositories with security alerts using security overview
The information shown by security overview varies according to your access to repositories and organizations, and according to whether GitHub Advanced Security is used by those repositories and organizations. For more information, see About security overview.
-
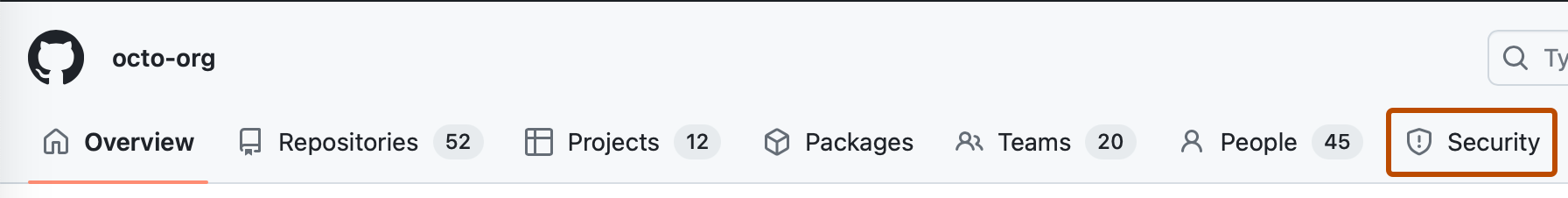
On GitHub, navigate to the main page of the organization.
-
Under your organization name, click Security.
-
By default, the overview shows alerts for all native GitHub tools (filter:
tool:github). To display alerts for a specific tool, replacetool:githubin the filter text box. For example:tool:dependabotto show only alerts for dependencies identified by Dependabot.tool:secret-scanningto only show alerts for secrets identified by secret scanning.tool:codeqlto show only alerts for potential security vulnerabilities identified by CodeQL code scanning.
-
You can add further filters to show only the repositories you want to assess. The list of repositories and metrics displayed on the page automatically update to match your current selection. For more information on filtering, see Filtering alerts in security overview.
- Use the Teams dropdown to show information only for the repositories owned by one or more teams.
- Click NUMBER affected or NUMBER unaffected in the header for any feature to show only the repositories with open alerts or no open alerts of that type.
- Click any of the descriptions of "Open alerts" in the header to show only repositories with alerts of that type and category. For example, 1 critical to show the repository with a critical alert for Dependabot.
- At the top of the list of repositories, click NUMBER Archived to show only repositories that are archived.
-
Optionally, use the sidebar on the left to explore alerts for a specific security feature in greater detail. On each page, you can use filters that are specific to that feature to refine your search. For more information about the available qualifiers, see Filtering alerts in security overview.
Interpreting secret scanning alerts
Secret scanning is a security tool that scans the entire Git history of repositories, as well as issues, pull requests, discussions, and wikis in those repositories, for leaked secrets that have been accidentally committed, such as tokens or private keys. There are two types of secret scanning alerts:
- Secret scanning alerts for partners, which are sent to the provider who issued the secret
- Secret scanning alerts for users, which appear on GitHub and can be resolved
You can view secret scanning alerts for an organization by navigating to the main page of that organization, clicking the Security tab, then clicking Secret scanning.
For an introduction to secret scanning alerts, see About secret scanning alerts.
To learn how to evaluate secret scanning alerts, see Evaluating alerts from secret scanning.
Interpreting code scanning alerts
Code scanning is a feature that you use to analyze the code in a GitHub repository to find security vulnerabilities and coding errors. Any problems identified by the analysis are shown in your repository. These problems are raised as code scanning alerts, which contain detailed information on the vulnerability or error detected.
You can view the code scanning alerts for an organization by navigating to the main page of that organization, clicking the Security tab, then clicking Code scanning.
For an introduction to code scanning alerts, see About code scanning alerts.
To learn how to interpret and resolve code scanning alerts, see Assessing code scanning alerts for your repository and Resolving code scanning alerts.
Interpreting Dependabot alerts
Dependabot alerts inform you about vulnerabilities in the dependencies that you use in repositories in your organization. You can view Dependabot alerts for an organization by navigating to the main page of that organization, clicking the Security tab, then clicking Dependabot.
For an introduction to Dependabot alerts, see About Dependabot alerts.
To learn how to interpret and resolve Dependabot alerts, see Viewing and updating Dependabot alerts.
Note
If you enabled Dependabot security updates, Dependabot can also automatically raise pull requests to update the dependencies used in the repositories of the organization. For more information, see About Dependabot security updates.
Next steps
If you are using the GitHub-recommended security configuration, and your findings indicate the security enablement settings are not meeting your needs, you should create a custom security configuration. To get started, see Creating a custom security configuration.
If you are using a custom security configuration, and your findings indicate the security enablement settings are not meeting your needs, you can edit your existing configuration. For more information, see Editing a custom security configuration.
Lastly, you can also edit your organization-level security settings with global settings. To learn more, see Configuring global security settings for your organization.